When My PC Suddenly Turned Into a Countdown Timer
If you were online in 2003, you probably remember this moment. I was sitting at my computer, Windows XP humming away, dial‑up screeching in the background when suddenly my screen froze and a Windows dialog box popped up:
“Windows must now restart because the Remote Procedure Call (RPC) service terminated unexpectedly.”
And then the countdown started. Sixty seconds.
No warning. Just a digital guillotine slowly dropping. I hadn’t clicked or installed anything. I was just connected to the internet.
That was the day the Blaster worm arrived.
My Life at the Time: TAFE, Cert IV, and Being “The Computer Guy”
Back then I was in my first year of TAFE, studying my Cert IV and already the unofficial tech support for everyone I knew. If someone’s PC fell over, they called me. If something weird popped up on their screen, they called me. If their computer made a noise they didn’t like, they called me.
So when I heard about Blaster, I did what any eager Cert IV student would do, I read everything I could about it. I knew the vulnerability, I knew the patch existed, and I knew it was only a matter of time before it hit me.
And then it did.
Dial‑Up: The Wild West of the Early Internet
I was on dial‑up at the time, which meant two things:
- The internet was painfully slow
- Everyone on dial‑up felt like they were on the same giant, unprotected LAN
No firewalls. No NAT. No isolation.
Just raw Windows XP machines sitting out in the open.
I could literally scan the dial‑up “network” and see other people’s shared folders. It was that exposed.
So of course Blaster found me instantly.
The First Infection
The shutdown timer appeared.
RPC crashed.
My machine started counting down from 60.
And here’s the funny part: I had no idea about the easy pause button “shutdown -a” back then. I wish I did. It would’ve saved me a lot of panic and a lot of dial‑up reconnects. My Dad had to pay for a lot of those dial‑up phone calls… sorry, Dad.
But at the time, all I could do was watch the timer tick down, swear under my breath, and brace for the reboot.
The Patch Quest: Five Shutdowns, One Download Manager, and a Lot of Determination
I knew the patch was out there, MS03‑026. But downloading anything on dial‑up was like trying to clip a CPU cooler onto a Pentium III.
I bookmarked the link, fired up one of those old download managers that saved partial progress, and started the download.
And then Blaster struck again. Shutdown timer. Reboot. Reconnect. Resume download.
It happened five times. Five dial‑up sessions. Five shutdown sequences. Five races against the clock.
Finally on the fifth attempt the download manager finished the patch file. My PC rebooted immediately after, as if Blaster wanted one last laugh.
I booted back up, ran the patch, and just like that… I’d beaten it.
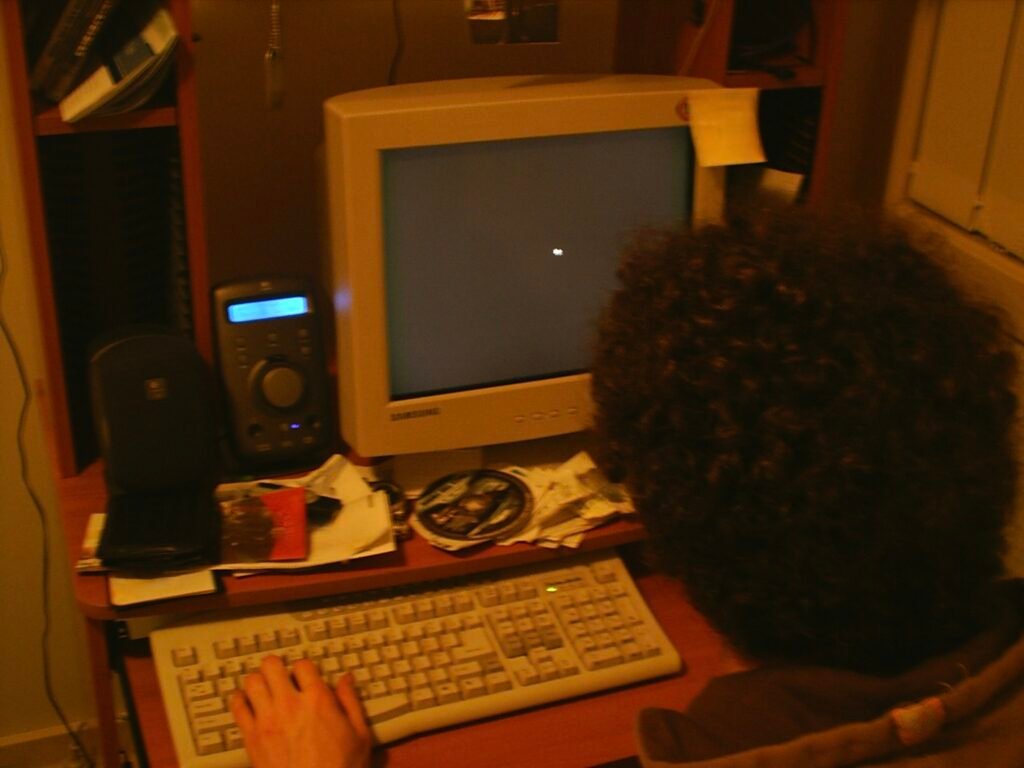
Throwback to My Actual 2003 Setup
Becoming the Blaster Patch Delivery Service
Once I had the patch, I felt like I was holding the cure to a digital plague. I walked around the house patching every PC. Then I helped friends. Then family.
Then anyone who could get through to me on the phone assuming I wasn’t online at the time.
It was chaotic, hilarious, and honestly one of the most fun early‑tech experiences I’ve ever had.
What Blaster Actually Exploited
Blaster targeted a vulnerability in Windows XP/2000’s RPC DCOM interface, allowing remote code execution with no authentication.
- CVE‑2003‑0352
- Microsoft Security Bulletin MS03‑026
Once inside, it crashed the RPC service, which triggered the 60‑second shutdown.
It spread automatically by scanning random IP addresses. No emails, downloads or user interactions. If you were online and unpatched, you were a target.
The Patch That Should Have Saved Everyone
Microsoft actually released the patch a month earlier, on 16 July 2003. But the early 2000s were a different world:
- Windows Firewall was off by default
- Automatic Updates wasn’t widely used
- Home users didn’t patch unless something broke
- Dial‑up users were basically naked on the internet
So when Blaster hit on 11 August 2003, millions of machines were still vulnerable. The worm even contained a message aimed at Bill Gates:
“Billy Gates, why do you make this possible? Stop making money and fix your software.”
Peak early‑internet energy.
Reflection: The Turning Point
Looking back, the Blaster worm wasn’t just an inconvenience, it was a turning point for me. Up until then, viruses were mostly a curiosity, a challenge to fix, something that came with the territory of being “the computer guy.” But Blaster was different. It didn’t arrive through an email attachment or a dodgy download. It came straight through the internet itself, hit my machine out of nowhere, and forced me to fight through multiple shutdowns just to stay online.
That was the moment I realised the threat landscape was bigger than I understood.
I was still in my Cert IV days, still figuring out where I fit in the world of IT, but Blaster opened my eyes. It pushed me to start collecting tools, utilities, patches, and anything I could use to protect systems, mine and everyone else’s. It wasn’t the first infection I ever remediated, but it was the first one that genuinely shocked me. The speed, the spread, the way it exploited a vulnerability most people didn’t even know existed, it changed how I thought about computers.
From that point on, patching wasn’t just maintenance, It became a responsibility.
I started caring about updates, firewalls, antivirus tools, and proper controls. I wanted to understand how and why things broke. That early experience sitting at my desk, fighting off a worm over dial‑up planted the seed for the IT career I thought I was building. I had no idea that this kind of work would eventually become its own field. Back then it was just “IT,” but moments like this were quietly shaping the direction my career would take.
References
These are the sources used to verify the technical details in this article:
- Microsoft Security Bulletin MS03‑026
- Blaster Worm (Technical Summary)
- CVE‑2003‑0352 – RPC DCOM Vulnerability